MCP Consent Infrastructure¶
Model Context Protocol as "robots.txt for AI" -- machine-readable permission queries that let AI platforms ask before using music.
The Simple Version¶
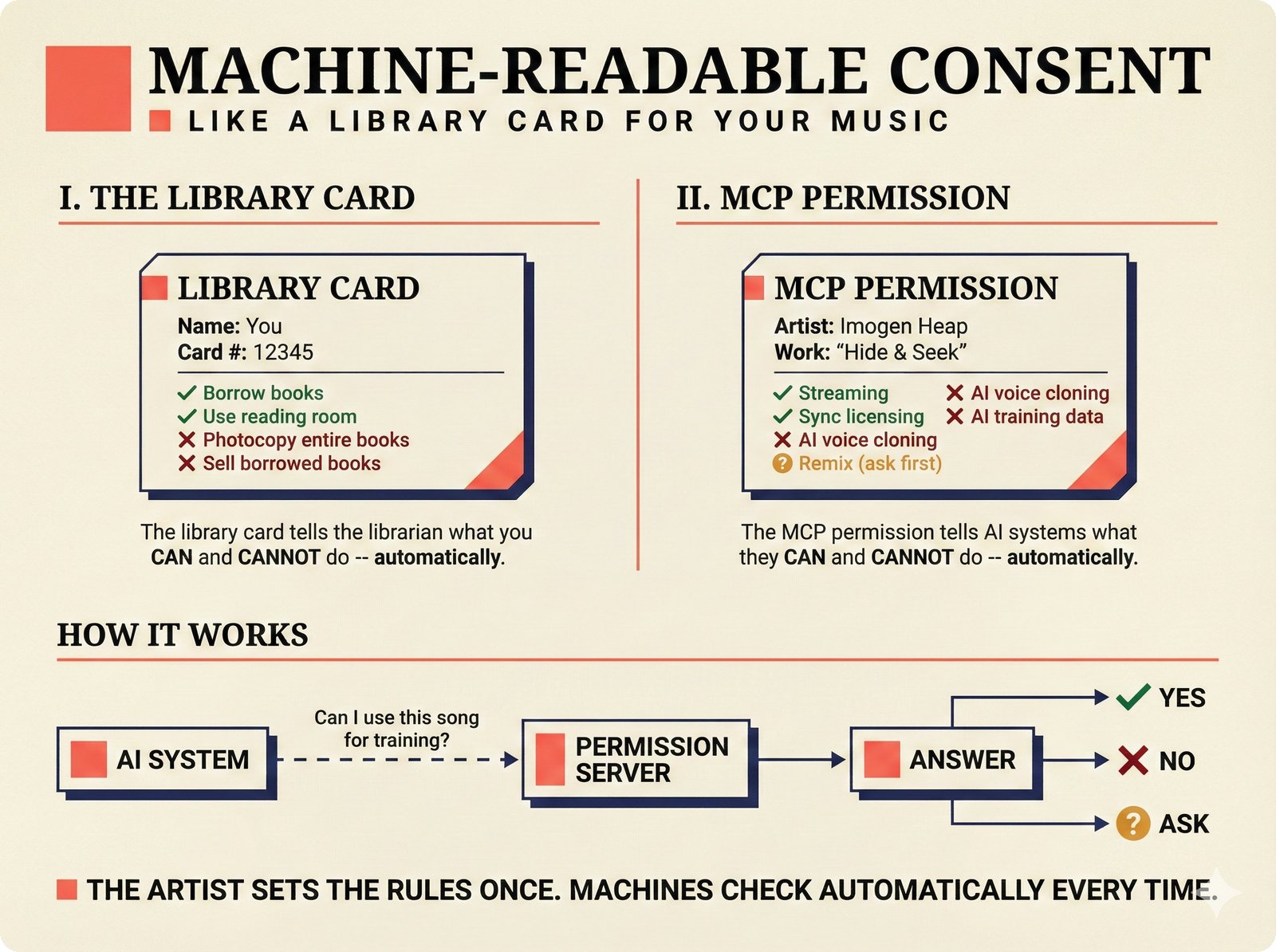
Figure 19. Machine-readable consent explained through a library card analogy: just as a library card specifies what you can and cannot do with borrowed books, MCP permissions let artists set specific rules for how AI systems can use their music -- set once, checked automatically every time.
You know how websites have a robots.txt file that tells search engines "you can index this page, but not that one"? It is a simple text file that machines read automatically, without any human needing to send an email or make a phone call.
Music needs the same thing for AI. Right now, if an AI company wants to know "can I use this song to train my model?", there is no machine-readable way to ask. They would have to email a label, wait weeks, and maybe get an answer. Or they just use the music without asking.
MCP (Model Context Protocol) creates a machine-readable permission system for music. An AI platform connects to a music catalog's MCP server and asks: "Can I use song X for AI training?" The server instantly replies with one of:
- ALLOW -- go ahead
- DENY -- no, do not use this
- ASK -- contact the rights holder
- ALLOW_WITH_ATTRIBUTION -- yes, but credit the artist
- ALLOW_WITH_ROYALTY -- yes, but pay this rate
No emails. No lawyers. No six-week delays. The answer is instant, machine-readable, and auditable.
The Drive-Through Analogy
Instead of parking, walking into a restaurant, and waiting to be seated (current licensing), MCP is a drive-through window. You pull up, ask what you want, get an answer, and move on. The menu is posted (machine-readable), the prices are clear, and the transaction is fast.
For Music Industry Professionals¶
How Artists Declare Permissions¶
The scaffold implements a Permission Patchbay -- a structured way for artists and rights holders to declare their preferences for every type of use:
Artists can set separate permissions for each use case:
| Permission Type | What It Covers |
|---|---|
AI_TRAINING |
General AI model training |
AI_TRAINING_COMPOSITION |
Training on the musical composition |
AI_TRAINING_RECORDING |
Training on the specific recording |
AI_TRAINING_STYLE |
Learning the artist's style |
VOICE_CLONING |
Cloning the artist's voice |
STYLE_LEARNING |
Learning stylistic patterns |
LYRICS_IN_CHATBOTS |
Displaying lyrics in AI chatbots |
DATASET_INCLUSION |
Including in research datasets |
SAMPLE |
Sampling in new works |
REMIX |
Remixing the work |
SYNC_LICENSE |
Synchronization with video |
DERIVATIVE_WORK |
Creating derivative works |
Each permission can have one of five values:
| Value | Meaning |
|---|---|
ALLOW |
Permitted, no conditions |
DENY |
Not permitted under any circumstances |
ASK |
Contact the rights holder for case-by-case approval |
ALLOW_WITH_ATTRIBUTION |
Permitted if the artist is credited |
ALLOW_WITH_ROYALTY |
Permitted if a royalty rate is paid |
Permissions can be set at different granularities:
| Scope | Example |
|---|---|
CATALOG |
"All of Imogen Heap's works" |
RELEASE |
"The album Speak for Yourself" |
RECORDING |
"The recording of Hide and Seek" |
WORK |
"The composition Hide and Seek" |
Delegation Chains¶
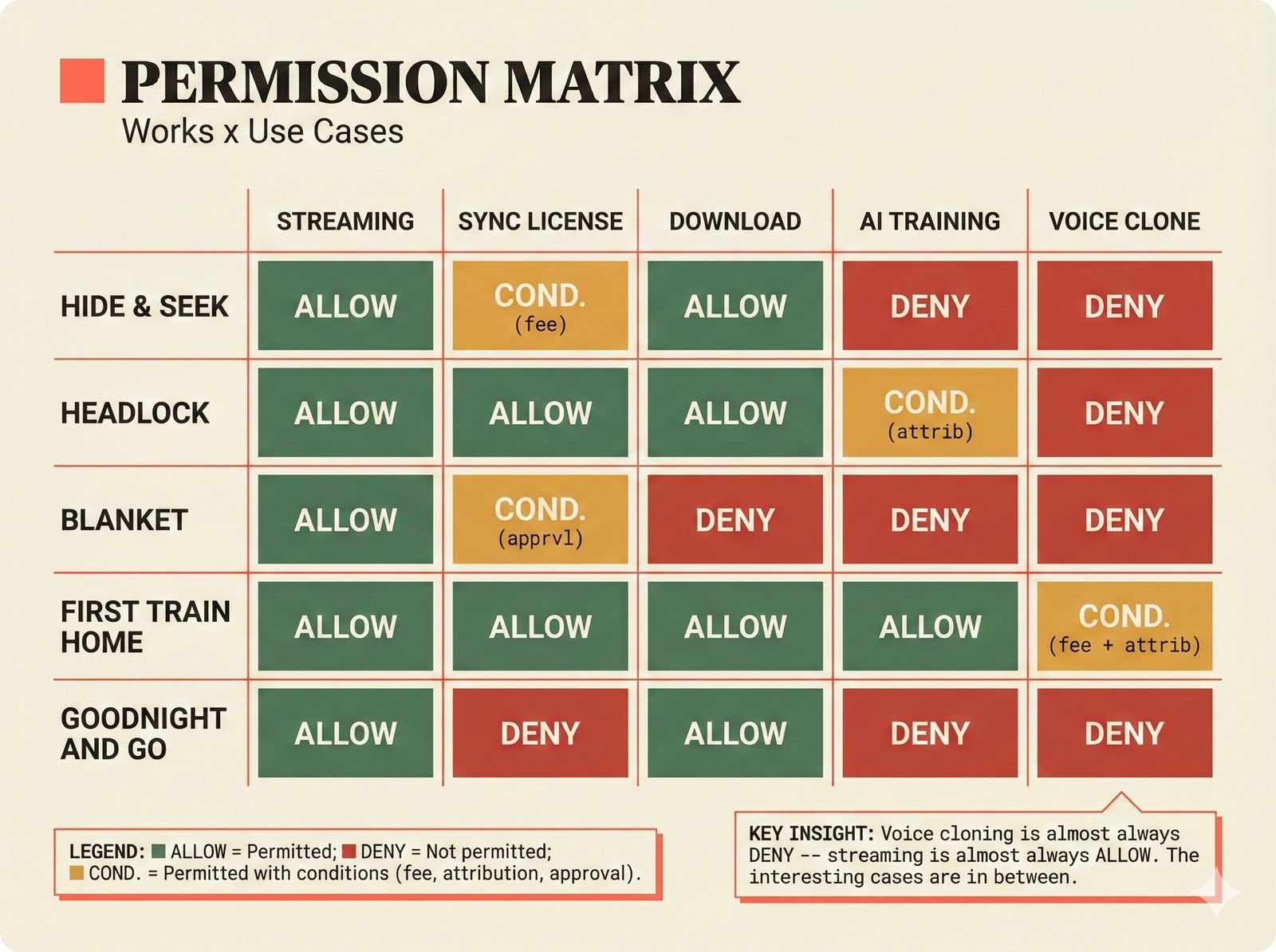
Figure 22. Permission matrix across works and use cases: permissions are not binary -- each musical work has a unique profile where streaming is typically allowed, voice cloning is typically denied, and the interesting policy decisions (AI training, sync licensing) vary per work with conditional terms.
In the music industry, permission decisions often flow through a chain: artist to manager to label to distributor. The scaffold tracks this with delegation entries:
Artist (Imogen Heap) → Manager (can_modify: true, can_delegate: true)
→ Label (can_modify: false, can_delegate: true)
→ Distributor (can_modify: false, can_delegate: false)
Each link in the chain specifies whether the delegate can modify permissions or further delegate authority.
The robots.txt Gap
Current rights reservation methods (robots.txt, LLMS_TXT) are web-only and do not cover audio content accessed via APIs or streaming platforms. The scaffold's TdmReservationMethodEnum includes MCP_PERMISSION_QUERY specifically to fill this gap.
Why This Matters Now¶
The EU's DSM Directive Article 4 allows copyright holders to opt out of text-and-data mining via "machine-readable reservation." The GPAI Code of Practice (July 2025) requires AI providers to respect these reservations. But music has no standardized, machine-readable way to declare them. MCP provides the infrastructure.
For Engineers¶
MCP Server Implementation¶
The scaffold's MCP server is implemented in src/music_attribution/mcp/server.py using the FastMCP framework:
# From src/music_attribution/mcp/server.py
class MCPAttributionServer:
"""MCP server for attribution and permission queries."""
def __init__(self) -> None:
self.name = "music-attribution"
self._mcp = FastMCP(self.name)
self._attributions: dict[uuid.UUID, AttributionRecord] = {}
self._permissions: dict[uuid.UUID, PermissionBundle] = {}
self._register_tools()
Tool Definitions¶
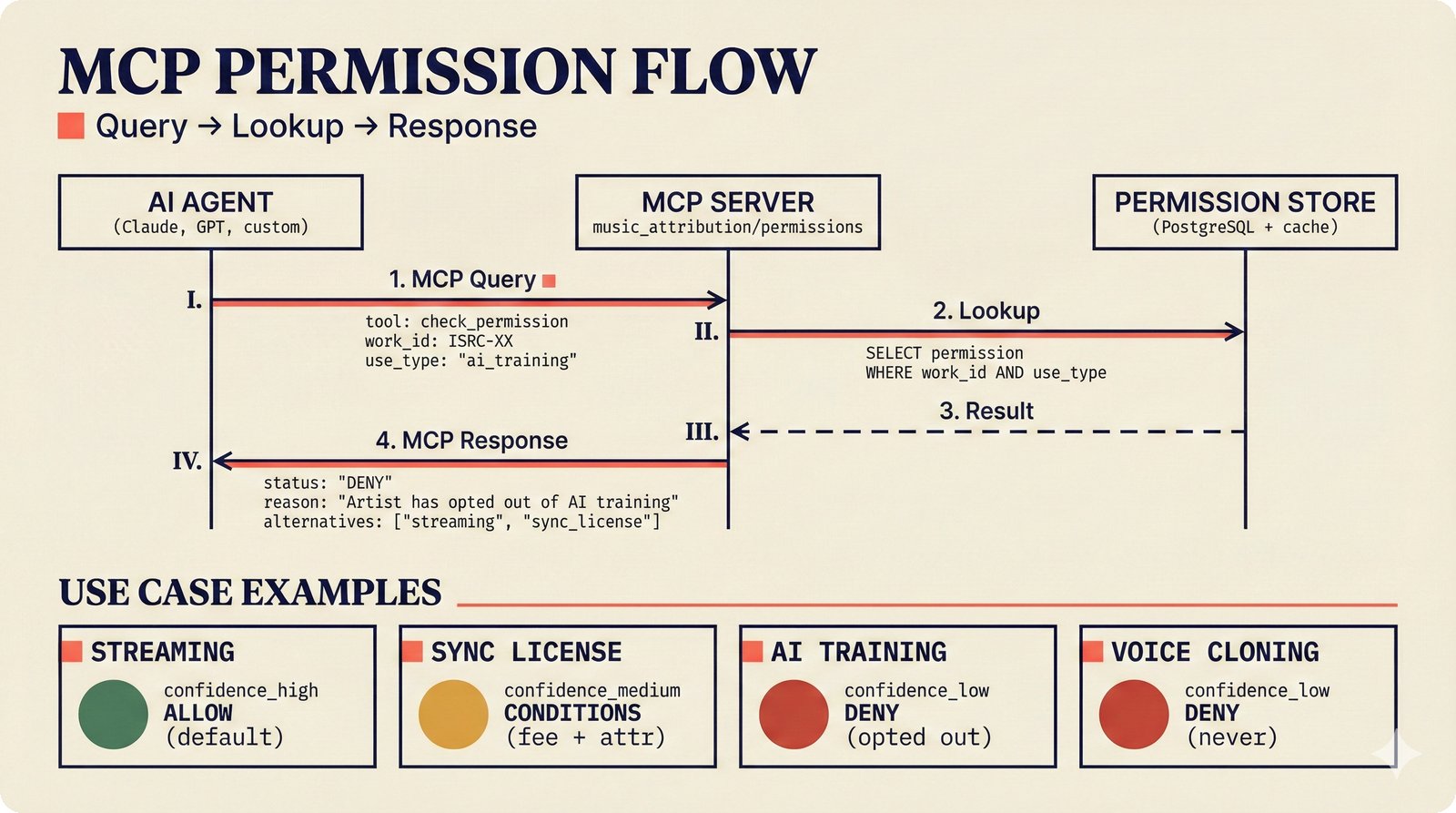
Figure 20. The MCP permission flow: an AI agent sends a structured query specifying work ID and intended use, the MCP server looks up the artist's permissions in PostgreSQL, and returns ALLOW, DENY, or CONDITIONS with machine-readable terms and suggested alternatives when denying.
The server exposes three tools that AI platforms can call:
graph LR
AI[AI Platform] -->|query_attribution| MCP[MCP Server]
AI -->|check_permission| MCP
AI -->|list_permissions| MCP
MCP -->|AttributionRecord| AI
MCP -->|PermissionValue| AI
MCP -->|PermissionBundle| AI
style AI fill:#e1f5fe,stroke:#0277bd
style MCP fill:#f3e5f5,stroke:#6a1b9aRetrieve the full attribution record for a work:
The PermissionBundle Schema¶
Each entity's permissions are stored as a PermissionBundle:
# From src/music_attribution/schemas/permissions.py
class PermissionBundle(BaseModel):
schema_version: str = "1.0.0"
permission_id: uuid.UUID
entity_id: uuid.UUID
scope: PermissionScopeEnum # CATALOG, RELEASE, RECORDING, WORK
permissions: list[PermissionEntry] # At least one entry
effective_from: datetime # When permissions become active
effective_until: datetime | None # Optional expiry
delegation_chain: list[DelegationEntry]
default_permission: PermissionValueEnum # Fallback for unset types
Individual permission entries can carry conditions:
class PermissionEntry(BaseModel):
permission_type: PermissionTypeEnum # AI_TRAINING, VOICE_CLONING, etc.
value: PermissionValueEnum # ALLOW, DENY, ASK, etc.
conditions: list[PermissionCondition] # Optional conditions
royalty_rate: Decimal | None # Required if ALLOW_WITH_ROYALTY
attribution_requirement: str | None # Required if ALLOW_WITH_ATTRIBUTION
territory: list[str] | None # Geographic restrictions
Validation Rules¶
The schema enforces consistency through Pydantic validators:
ALLOW_WITH_ROYALTYrequiresroyalty_rate > 0ALLOW_WITH_ATTRIBUTIONrequires non-Noneattribution_requirementCATALOGscope requiresscope_entity_idto be None- Non-catalog scopes require
scope_entity_idto be set - All timestamps must be timezone-aware (UTC)
effective_frommust be beforeeffective_until
TDM Reservation Methods¶
The scaffold tracks how rights are reserved across different protocols:
# From src/music_attribution/schemas/enums.py
class TdmReservationMethodEnum(StrEnum):
ROBOTS_TXT = "ROBOTS_TXT" # Web-only, text/data mining
LLMS_TXT = "LLMS_TXT" # LLM-specific extension
MACHINE_READABLE_TAG = "MACHINE_READABLE_TAG" # HTML meta tags
RIGHTS_RESERVATION_API = "RIGHTS_RESERVATION_API" # Programmatic API
MCP_PERMISSION_QUERY = "MCP_PERMISSION_QUERY" # This scaffold's approach
Design Principle
The scaffold positions MCP as the most complete reservation method because it is bidirectional (query and response), structured (typed permissions, not just allow/deny), and auditable (provenance chain on every query).
Integration Architecture¶
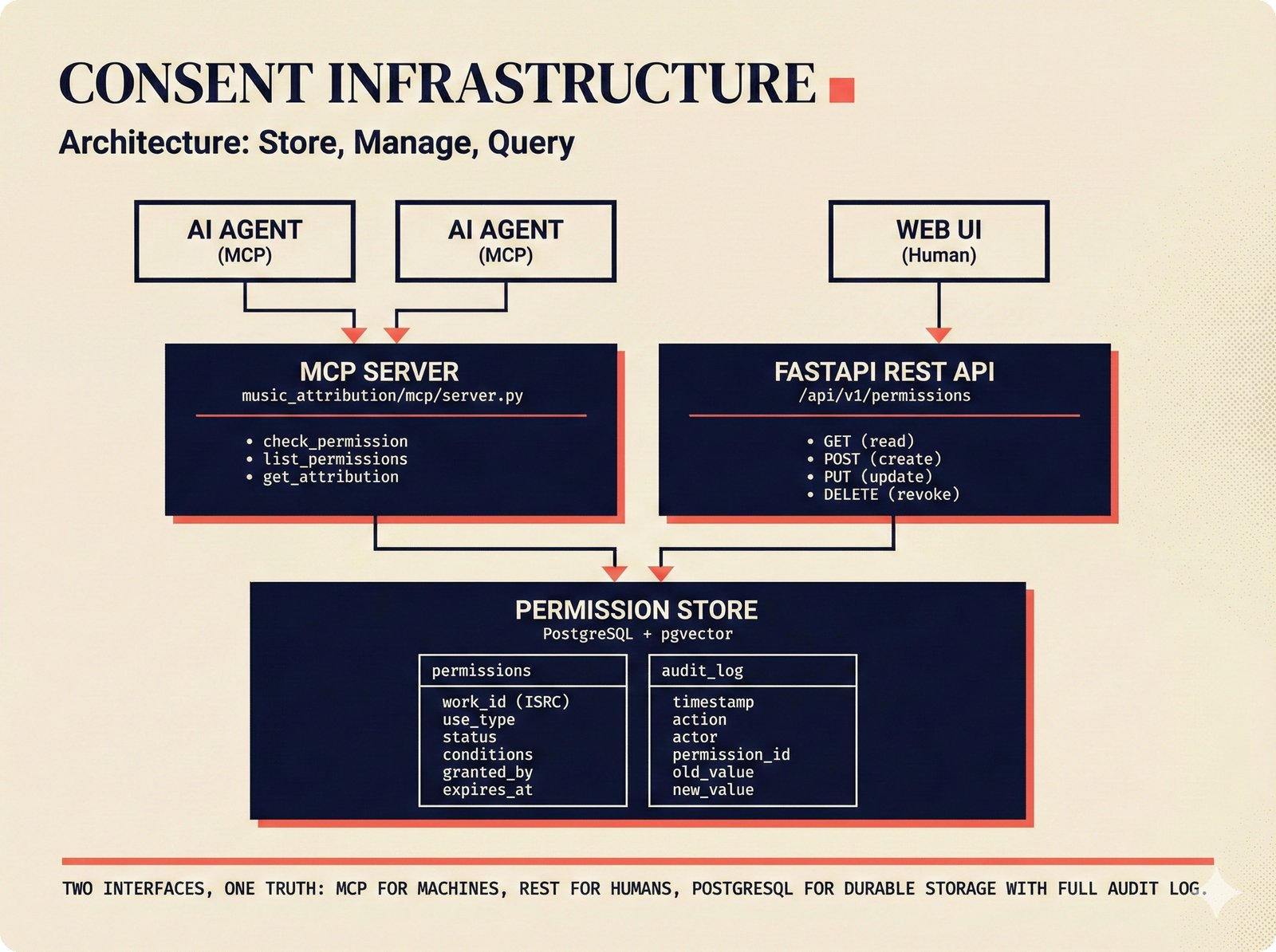
Figure 21. Consent infrastructure architecture: two interfaces (MCP for machine-to-machine queries, FastAPI REST for human management) share a single PostgreSQL permission store with full audit logging, embodying the principle of "two interfaces, one truth" for durable consent management.
graph TD
Artist[Artist / Rights Holder] -->|sets permissions| PB[PermissionBundle]
Manager[Manager / Label] -->|delegates| PB
PB -->|stored in| DB[(PostgreSQL)]
DB -->|served by| MCP[MCP Server]
MCP -->|check_permission| AI1[AI Training Platform]
MCP -->|check_permission| AI2[Music Generator]
MCP -->|list_permissions| AI3[Licensing Service]
MCP -->|query_attribution| Chat[Chat Agent]
Chat -->|displays to| User[Human User]
style Artist fill:#fff3e0,stroke:#e65100
style MCP fill:#f3e5f5,stroke:#6a1b9a
style AI1 fill:#e1f5fe,stroke:#0277bd
style AI2 fill:#e1f5fe,stroke:#0277bd
style AI3 fill:#e1f5fe,stroke:#0277bdKey Source Files¶
| File | Role |
|---|---|
src/music_attribution/mcp/server.py |
MCPAttributionServer with three tools |
src/music_attribution/schemas/permissions.py |
PermissionBundle, PermissionEntry, DelegationEntry |
src/music_attribution/schemas/enums.py |
PermissionTypeEnum, PermissionValueEnum, TdmReservationMethodEnum |
src/music_attribution/schemas/compliance.py |
ComplianceAttestation for Fairly Trained, C2PA, EU AI Act |
How This Maps to Code¶
The MCP consent infrastructure connects four layers of the scaffold:
- Schemas define the permission vocabulary (16 permission types, 5 values, 4 scopes)
- MCP Server exposes three tools for querying permissions and attribution
- API layer serves the same data over REST for non-MCP consumers
- Frontend displays permission status alongside attribution records
Paper Citation
"MCP transforms consent from a bilateral negotiation (email chains, PDF contracts) into a multilateral infrastructure (machine-readable, auditable, instant). This is the difference between a customs checkpoint and a free-trade zone." -- Teikari (2026), Section 5.3